In our case the Phantom DLL hijacking technique works because Wacom_Tablet.exe doesn't use signed DLLs or particular DLL hijacking prevention techniques.
Read this article if you want to learn more about some DLL hijacking prevention techniques.
Read this article of mine if you want to learn more about the DLL Hijacking using the DLL Proxying technique.
Different ways to escalate our privileges ↖️⬆️↗️
To escalate the privileges I decided to use the technique just described (which I will deepen in the next paragraph) to enhance the discovery of the phantom dll and to illustrate an alternative way to the one followed in ZDI-CAN-16318.
However, there are other ways to take advantage of the Arbitrary File Write primitive to escalate privileges and, among them, I want to describe the following two:
-
Overwrite
C:\Program Files\Tablet\Wacom\32\Installer.dat
Similarly to what I did here we can abuse the Installer.dat file to run an arbitrary program but, in this case, everything is much easier because we can exploit an Arbitrary File Write primitive (and not an Arbitrary File Write primitive with partial control over the content of the file written\overwritten).
We can exploit the Arbitrary File Write primitive previously described to overwrite Installer.dat with another identical file to which the following line has been added:

At this point the regular user only needs to restore a backup of his Wacom device through "C:\Program Files\Tablet\Wacom\PrefUtil.exe" /restore "C:\...\Backup.wacomprefs" /silent to force Remove.exe to execute the UpdateRouterFilter command which, consequently, will execute a command prompt window under the context of SYSTEM.
-
Overwrite
C:\Program Files\Tablet\Wacom\32\Remove.exe
Instead of overwriting Installer.dat we can directly overwrite (exploiting the Arbitrary File Write primitive previously described) Remove.exe with a simple executable which, once started, will execute a command prompt window, like this one:
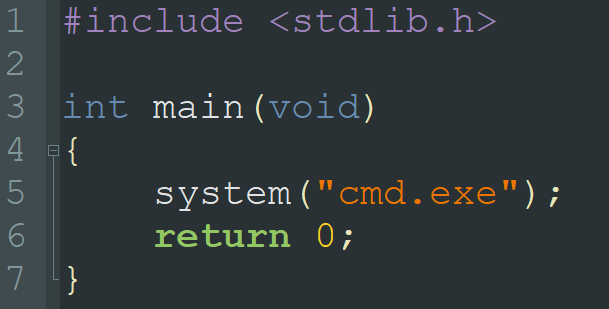
At this point the regular user only needs to restore a backup of his Wacom device through "C:\Program Files\Tablet\Wacom\PrefUtil.exe" /restore "C:\...\Backup.wacomprefs" /silent to force Wacom_Tablet.exe (which runs under the context of SYSTEM) to execute Remove.exe which, consequently, will execute a command prompt window under the same context.
The negative side of this technique is to make it impossible for Remove.exe to carry out all the operations it has to perform once started (since we have replaced it), while the previous technique is not affected by this problem because it simply forces Remove.exe to perform one more operation (the execution of the command prompt window) than the ones it has to execute normally.
C:\Program Files\Tablet\Wacom\32\Installer.datSimilarly to what I did here we can abuse the
Installer.dat file to run an arbitrary program but, in this case, everything is much easier because we can exploit an Arbitrary File Write primitive (and not an Arbitrary File Write primitive with partial control over the content of the file written\overwritten).We can exploit the Arbitrary File Write primitive previously described to overwrite
Installer.dat with another identical file to which the following line has been added:
At this point the regular user only needs to restore a backup of his Wacom device through
"C:\Program Files\Tablet\Wacom\PrefUtil.exe" /restore "C:\...\Backup.wacomprefs" /silent to force Remove.exe to execute the UpdateRouterFilter command which, consequently, will execute a command prompt window under the context of SYSTEM.
C:\Program Files\Tablet\Wacom\32\Remove.exeInstead of overwriting
Installer.dat we can directly overwrite (exploiting the Arbitrary File Write primitive previously described) Remove.exe with a simple executable which, once started, will execute a command prompt window, like this one: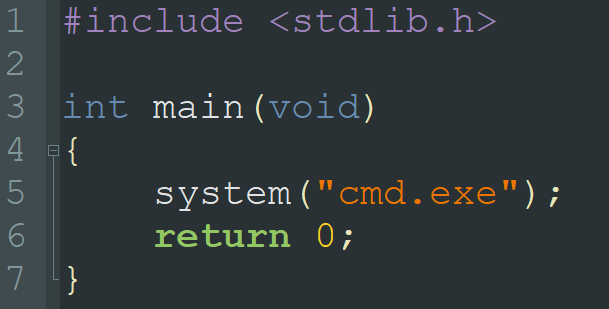
At this point the regular user only needs to restore a backup of his Wacom device through
"C:\Program Files\Tablet\Wacom\PrefUtil.exe" /restore "C:\...\Backup.wacomprefs" /silent to force Wacom_Tablet.exe (which runs under the context of SYSTEM) to execute Remove.exe which, consequently, will execute a command prompt window under the same context.The negative side of this technique is to make it impossible for
Remove.exe to carry out all the operations it has to perform once started (since we have replaced it), while the previous technique is not affected by this problem because it simply forces Remove.exe to perform one more operation (the execution of the command prompt window) than the ones it has to execute normally.
The Exploit ☠️
The exploit that I've implemented and that I'm going to describe is based on the previously described technique, and performs the following steps:
-
If the
C:\Wacom folder exists, delete it and re-create it; create it otherwise.
-
Create the
C:\Wacom\Logs mount point to \RPC Control.
-
Create the
\RPC Control\WacomTouch.xml.txt symbolic link to %ProgramFiles%\Tablet\Wacom\FTD2XX.dll.
-
Copy the malicious
FTD2XX.dll to %AppData%\WTablet\WacomTouch.xml.
-
Run
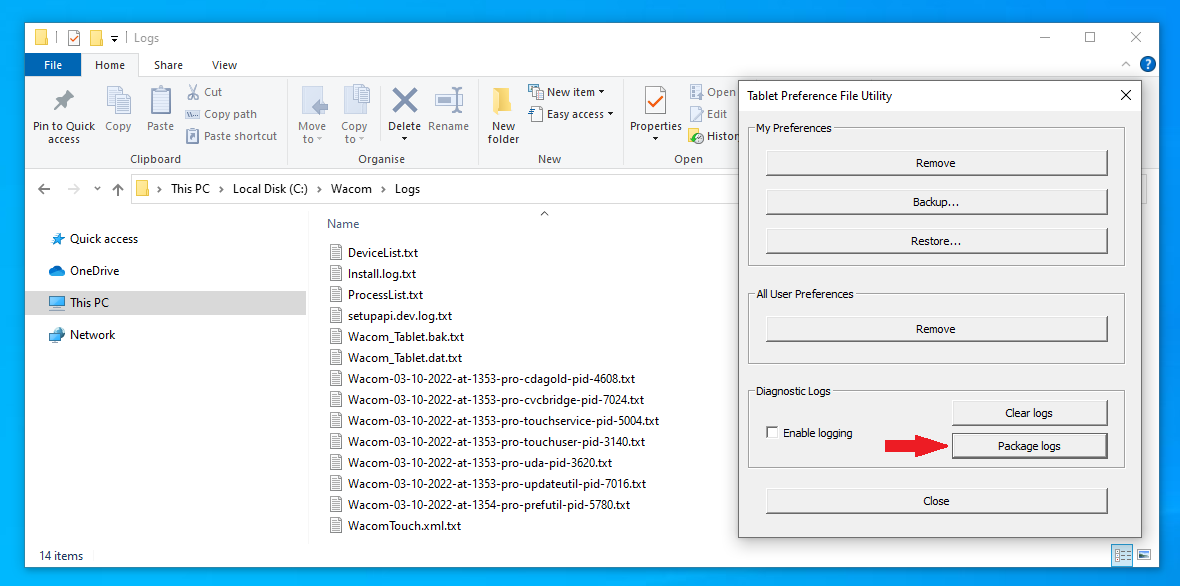
PrefUtil.exe through %ProgramFiles%\Tablet\Wacom\PrefUtil.exe /package-logs.
The following operations are performed:
-
PrefUtil.exe starts to package the logs into C:\Wacom\Logs.
-
WTabletServicePro.exe, running under the context of SYSTEM, tries to copy %AppData%\WTablet\WacomTouch.xml to C:\Wacom\Logs\WacomTouch.xml.txt without impersonating the current user.
-
Since
C:\Wacom\Logs is a mount point to \RPC Control, WTabletServicePro.exe tries to copy %AppData%\WTablet\WacomTouch.xml to \RPC Control\WacomTouch.xml.txt.
-
Since
\RPC Control\WacomTouch.xml.txt is a symbolic link to %ProgramFiles%\Tablet\Wacom\FTD2XX.dll, WTabletServicePro.exe copies %AppData%\WTablet\WacomTouch.xml to %ProgramFiles%\Tablet\Wacom folder and names it FTD2XX.dll.
-
Run
PrefUtil.exe through C:\Program Files\Tablet\Wacom\PrefUtil.exe /silent /remove.
The following operations are performed silently:
-
PrefUtil.exe performs several operations and Wacom_Tablet.exe is triggered.
-
Wacom_Tablet.exe performs several operations and tries to load the %ProgramFiles%\Tablet\Wacom\FTD2XX.dll dll.
-
Since
FTD2XX.dll now exists (point 5.4), it's loaded into memory and executed (without any checks).
-
FTD2XX.dll is programmed to execute a command prompt window and, since it's loaded from Wacom_Tablet.exe (which runs under the context of SYSTEM), the command prompt will also run under the same context, allowing us to escalate our privileges 🎉
Here you can find the C# source code of my exploit (Visual Studio Project.zip).
Here you can find the executable file (Exploit.exe).
CreateMountPoint.exe and CreateSymlink.exe are programs developed by James Forshaw and are downloadable from his symboliclink-testing-tools repository, respectively here and here.
C:\Wacom folder exists, delete it and re-create it; create it otherwise.
C:\Wacom\Logs mount point to \RPC Control.
\RPC Control\WacomTouch.xml.txt symbolic link to %ProgramFiles%\Tablet\Wacom\FTD2XX.dll.
FTD2XX.dll to %AppData%\WTablet\WacomTouch.xml.
PrefUtil.exe through %ProgramFiles%\Tablet\Wacom\PrefUtil.exe /package-logs.The following operations are performed:
-
PrefUtil.exestarts to package the logs intoC:\Wacom\Logs. -
WTabletServicePro.exe, running under the context of SYSTEM, tries to copy%AppData%\WTablet\WacomTouch.xmltoC:\Wacom\Logs\WacomTouch.xml.txtwithout impersonating the current user. -
Since
C:\Wacom\Logsis a mount point to\RPC Control,WTabletServicePro.exetries to copy%AppData%\WTablet\WacomTouch.xmlto\RPC Control\WacomTouch.xml.txt. -
Since
\RPC Control\WacomTouch.xml.txtis a symbolic link to%ProgramFiles%\Tablet\Wacom\FTD2XX.dll,WTabletServicePro.execopies%AppData%\WTablet\WacomTouch.xmlto%ProgramFiles%\Tablet\Wacomfolder and names itFTD2XX.dll.
PrefUtil.exe through C:\Program Files\Tablet\Wacom\PrefUtil.exe /silent /remove.The following operations are performed silently:
-
PrefUtil.exeperforms several operations andWacom_Tablet.exeis triggered. -
Wacom_Tablet.exeperforms several operations and tries to load the%ProgramFiles%\Tablet\Wacom\FTD2XX.dlldll. -
Since
FTD2XX.dllnow exists (point 5.4), it's loaded into memory and executed (without any checks). -
FTD2XX.dllis programmed to execute a command prompt window and, since it's loaded fromWacom_Tablet.exe(which runs under the context of SYSTEM), the command prompt will also run under the same context, allowing us to escalate our privileges 🎉